Content Security Policy
- 4 minutes to read
A Content Security Policy (CSP) is an additional layer of security built into most modern browsers. It allows the browser to recognize and mitigate certain types of risks, including Cross Site Scripting (XSS) and data injection attacks. These attacks include, but are not limited to, data theft, page spoofing, and malware distribution.
The CSP defines a list of policies/directives and initial values that specify which resources your site will allow/disallow.
To enable CSP protection, use the <meta> tag and explicitly define allowed functions using CSP directives.
You can only specify the default fetch directive to enable CSP:
<meta http-equiv="Content-Security-Policy" content="default-src 'self'">
This policy prevents the proper functioning of DevExpress Reporting components. DevExpress Reports will require additional permissions, as described below.
Directives for Reporting Components
The following meta tag specifies minimum required directives for DevExpress Reporting components:
<head>
<!--...-->
<meta http-equiv="Content-Security-Policy" content="default-src 'self';
img-src data: https: http:;
script-src 'self' 'unsafe-inline';
style-src 'self' 'unsafe-inline';
connect-src 'self';
worker-src 'self' blob:;
frame-src 'self' blob:;" />
<!--...-->
</head>
default-src 'self';- Fallback for other fetch directives.
img-src data: https: http:;- Allows the components to load specific images and document pages.
script-src 'self' 'unsafe-inline';Allows only scripts loaded from the same source as the current page protected with CSP.
Note
Blazor WebAssembly applications require the
unsafe-evalrule in thescript-srcdirective.Refer to the following article for more information: Enforce a Content Security Policy for ASP.NET Core Blazor.
style-src 'self' 'unsafe-inline';- Allows the use of inline style elements.
connect-src 'self' (optional) 'http:my_backend_url';- The optional
my_backend_urlvalue specifies the server endpoint. This is necessary for JavaScript-Based Reporting apps when client and server applications have different URLs. worker-src 'self' blob:;- Required for printing.
frame-src 'self' blob: (optional) 'http:my_backend_url';- Required for printing. The optional
my_backend_urlvalue specifies the server endpoint. This is necessary if client and server applications have different URLs.
Troubleshooting
Error with ‘unsafe-eval’ Directive
The use strict directive in scripts may generate a “Refused to evaluate a string as JavaScript because ‘unsafe-eval’ is not an allowed source of script…” error.
To address this error, include the Knockout library in the global scope and use an alias to reference the library.
For Angular applications:
Add the Knockout library to the page:
<script src="https://cdnjs.cloudflare.com/ajax/libs/knockout/3.5.1/knockout-latest.js"></script>Create the
src/knockout_global.jsfile with the following content:module.exports = window['ko'];Specify paths in the tsconfig.json file:
{ //... "compilerOptions": { //... "paths": { "knockout": ["src/knockout_global.js"] }, //... }, //... }
Custom Templates Do Not Work
DevExpress Reporting custom templates are based on the Knockout JavaScript library. The Knockout library uses the data-bind attribute to render a value in the following manner: it generates a function as a JavaScript string and passes the string to the new Function constructor.
To function properly, Knockout templates require the script-src 'unsafe-eval' CSP directive.
Important
We do not recommend the inclusion of the script-src 'unsafe-eval' directive in your content security policy. This directive may introduce a vulnerability as it enables script execution from a string on your page.
DevExpress Reporting stores JavaScript functions related to data-bind attributes in the cache, thus eliminating the need to run the script on the page. Our components do not need the ‘unsafe-eval’ directive.
Follow the steps below to use custom templates.
Call the addToBindingsCache Function
To add a custom template to the function cache, call the addToBindingsCache function before the component is rendered. You can handle the BeforeRender event to call the function.
Example: DevExtreme Template
<div data-options="dxTemplate: { name: 'content' }"></div>Example: Knockout Binding
<div data-bind="text: text, attr: { title: text }"></div>
Use the CLI Utility
v22.2 ships with our @devexpress/analytics-core-cli CLI utility package. It includes the processBindings command. You can use this command to automatically generate a file with the code that calls the addToBindingsCache function to add your templates to the cache.
Run the following command to install the package:
npm i @devexpress/analytics-core-cli
To process custom templates, execute the following command:
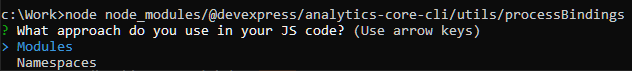
node node_modules/@devexpress/analytics-core-cli/utils/processBindings <templates folder path> <result file path>
Command parameters are as follows:
- templates folder path
- A folder that contains template files (.HTML)
- result file path
- Path to the file being created
When prompted, select application type (Modules or Namespaces):
The generated file contains JavaScript code that must be run in the DevExpress Reporting component’s BeforeRender event handler.