Data Access Security in WinForms Applications
- 5 minutes to read
This document describes how to avoid possible security risks when accessing data in reporting applications.
Important
The End-User Report Designer’s initial settings ensure a high level of database security.
We strongly recommend that you utilize the default behavior if your reporting application can be accessed by untrusted parties.
We also recommend that you use the access control functionality of your database management system to achieve the highest level of database security.
SQL Data Sources
Consider the security measures listed below if your application connects to SQL data sources. Utilize the access control functionality of your database management system for the highest level of database security.
Disable Custom SQL Queries
The Data Source Wizard initially allows only SQL queries visually designed in the built-in Query Builder. The Query Builder can construct only SELECT queries that are safe.
Default security settings do not allow you to edit SQL query text directly. When you invoke the Query Editor window, the text editor is disabled:

Enable SQL editing at your own risk as described in the following topic: Custom SQL Query in Report Designer (WinForms).
Validate Custom SQL Queries
Custom SQL queries are validated before their execution. Although the default validation mechanism only allows custom queries with SELECT statements (except for SELECT INTO clauses), it is not safe as it does not prevent execution of potentially harmful requests. You should implement secure SQL validation before you allow custom SQL queries.
To validate custom SQL for all queries created in your applications, handle the SqlDataSource.ValidateCustomSqlQueryGlobal static event.
For more information, review the following help topic: Custom SQL Query Validation (WinForms).
Manage Access Control at the Database Level
Do not use custom SQL query verification as the only security precaution. We recommend that you manage database security at the database level through appropriate access configuration and related options. By setting permissions within the database, you ensure that only authorized users and processes can access or modify data.
Protect Connection Password
The password part of the connection string is protected in the following ways:
The password characters are displayed as dots in the Connection Editor dialog:

In a custom connection string, the password is obscured with asterisk characters (the number of characters does not correspond to the actual length of the password).

In the Properties window, the username is not shown and the password is obscured with asterisk characters:

Do Not Serialize Sensitive Info
Set the DataConnectionBase.StoreConnectionNameOnly property to true, to serialize only database connection names. This guarantees that the database credentials are never exposed in report layout definitions (REPX files).
The initial value of the DataConnectionBase.StoreConnectionNameOnly property is false. In this situation, use the SqlWizardSettings.DatabaseCredentialsSavingBehavior and IConnectionStorageService.CanSaveConnection properties to specify how sensitive information is saved.
Important
If you have not yet done so, be sure to review the following help topic: DevExpress Reporting - Security Considerations.
Entity Framework Data Sources
Consider the security measures listed below if your application connects to Entity Framework data sources.
Restrict Access to Unauthorized Assemblies
Initial settings do not allow the reporting application to load custom assemblies referenced by Entity Framework data sources. To allow the application to load a specific assembly, handle the EFDataSource.BeforeLoadCustomAssembly event (or static EFDataSource.BeforeLoadCustomAssemblyGlobal event) and specify the following properties:
- AllowLoading
- Specifies whether the application is allowed to load a custom assembly.
- AssemblyPath
- Specifies the path to a requested assembly.
- ContextName
- Specifies the type to load from a custom assembly.
An unauthorized attempt to load a custom assembly throws the CustomAssemblyLoadingProhibitedException.
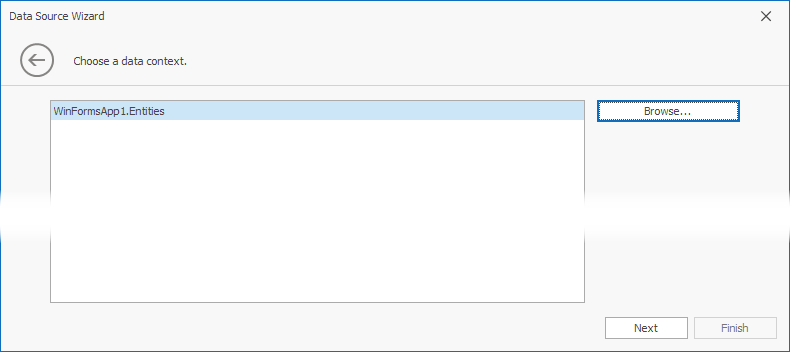
The Data Source Wizard for the Entity Framework allows you to load a custom assembly with the Browse button on the Choose a Data Context page. This button is hidden in the End-User Report Designer, and users are only allowed to select the data context from assemblies referenced in the project.

To make the Browse button visible, set the EFWizardSettings.ShowBrowseButton property to true.
Protect Connection Password
In the End-User Report Designer, the password portion of the connection string is obscured with asterisk characters (the number of characters does not correspond to the actual length of the password).
The Properties window:

The Data Source wizard (when you replace Entity Framework Data Source settings with a custom connection string):

Restrict Access to External Resources
Ensure that reports from untrusted sources cannot use the DataSource or XmlDataPath property to access the file system and read files. Restrictions affect ExcelDataSource and JsonDataSource data sources.
You can use static properties and methods of the AccessSettings class to explicitly specify file operation restrictions for Excel data sources and specify allowed URLs for JSON data sources. If your application does not retrieve data from file-based data sources, add the DirectoryAccessRule.Deny() access rule to the AccessSettings.DataResources settings to prohibit all file operations with data sources (review the following code snippet for more information):
// JSON data can be loaded only from URLs; Excel data cannot be loaded from file directories (Excel data load from URLs is not supported)
bool success = DevExpress.Security.Resources.AccessSettings.DataResources.SetRules(
DevExpress.Security.Resources.UrlAccessRule.Allow(),
DevExpress.Security.Resources.DirectoryAccessRule.Deny()) ;
if (!success) System.Diagnostics.Debug.Print("Cannot change rules. The rules are already set.")