Security - What You Need to Know
- 7 minutes to read
The following article is intended to support customer security, compliance, and software supply‑chain due‑diligence activities/requirements. This article addresses a series of frequently asked security-related questions and documents the processes we have established to mitigate security-related risk. It also includes links to Best Practice articles for various development platforms and products.
What We Do to Mitigate Risk
A team of developers – the DevExpress Security Guild – reviews all DevExpress technologies, new DevExpress solutions, and existing DevExpress products for security-related vulnerabilities. The Security Guild updates each product team regarding potential vulnerabilities and manages the on-going implementation of the following security-related testing strategies:
Prevention
Our primary goal is to isolate and address security-related issues before product delivery. We use the following prevention techniques to meet this objective:
Internal Registry of “Vulnerable” APIs
We maintain our own “vulnerable” API registry. This registry helps us locate and review questionable API calls and to mitigate potential security issues prior to official release. Our internal Security Guild tracks “vulnerable” C# API calls with assistance from the DevExpress IDE Productivity Team (developers of CodeRush and experts in code parsing techniques).
This prevention technique is used in the following products (v19.2 and later):
- DevExpress WinForms Subscription
- DevExpress ASP.NET Subscription
- DevExpress WPF Subscription
- UWP (Windows 10 Apps) Subscription
- Office File API Subscription
- Reporting Subscription
- DXperience Subscription
- Universal Subscription
- Business Intelligence Dashboard
- Cross-Platform .NET App UI (XAF)
- .NET Role-based Access Control API powered by EF Core and XPO ORM
- WinUI Controls
- .NET MAUI Controls
- Xamarin Forms UI Controls
Third-Party Static Analysis Testing: Veracode
We use Veracode’s static security scanner to analyze DevExpress source code. We review all Veracode-reported issues, fix vulnerabilities, and discard false positives.
You can review our Veracode Verified certificates on the following website:
https://www.veracode.com/verified/directory/devexpress
This prevention technique is used for the following .NET Framework, .NET Core, and UWP products/product suites by DevExpress.
- DevExpress WinForms Subscription
- DevExpress ASP.NET Subscription
- DevExtreme Complete Subscription
- DevExpress WPF Subscription
- UWP (Windows 10 Apps) Subscription
- Office File API Subscription
- Reporting Subscription
- DXperience Subscription
- Universal Subscription
- Business Intelligence Dashboard
- Cross-Platform .NET App UI (XAF)
- .NET Role-based Access Control API powered by EF Core and XPO ORM
- WinUI Controls
- .NET MAUI Controls
- Xamarin Forms UI Controls
Third-Party Testing Tool: CodeQL
DevExtreme (our JavaScript UI widgets for jQuery, Angular, React, and Vue) and TestCafe teams (our end-to-end/functional testing framework), utilize GitHub’s CodeQL continuous security analysis service. This service has been integrated into relevant team CI workflows and is used to analyze all merge requests submitted to associated repositories automatically.
Third-Party Dependency Scanning
GitHub Dependabot helps isolate security-related issues/vulnerabilities for dependencies (dependencies are listed within the DevExtreme and/or TestCafe End User License Agreement). Dependabot version updates include automated pull requests designed to update dependencies, even when they don’t include vulnerabilities.
We also leverage custom scan routines to validate NuGet dependencies referenced by DevExpress .NET Framework/.NET Core libraries and/or UI components. This allows us to address vulnerabilities in these dependencies based on publicly available vulnerability reports.
Independent Third-Party Pen Testing
DevExpress employs the services of independent cyber security consulting firm to manually test DevExpress UI component libraries. Time-boxed risk-based security reviews seek to identify/isolate vulnerabilities that may be used by threat actors to compromise DevExpress-powered applications. In addition to product-specific pen-testing, DevExpress uses independent security consultants to test and assess the resiliency of our internal IT infrastructure/internal network resources, and the security posture of DevExpress public-facing network resources.
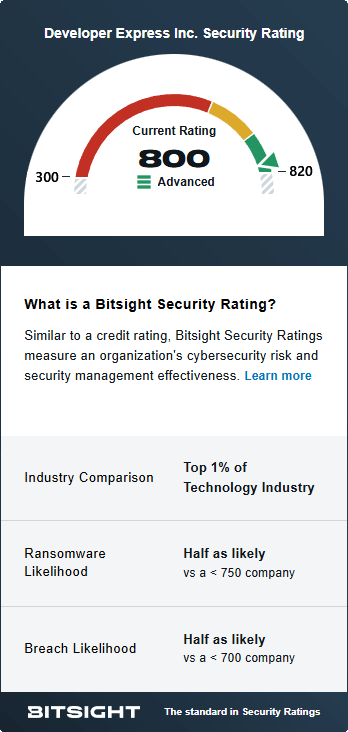
AI-powered Third-Party Cyber Risk Management
DevExpress utilizes multiple third-party network/infrastructure risk management tools, including BitSight.
Anti-Virus Testing: Installations/Official Distributions
Before publishing an official build, DevExpress installers/installations/libraries are tested against VirusTotal.
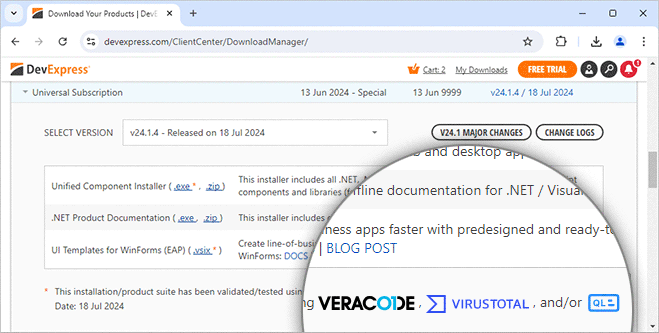
VirusTotal uses 70+ commercial anti-virus/malware scanners and crowdsourced detection tools.
DevExpress VirusTotal reports are available for review (sample report).
Anti-Virus Testing: Support Center Tickets
All support ticket attachments (images/videos/etc) submitted via the DevExpress Support Center are automatically scanned by anti-virus software.
Third-Party Testing Tool: NuGet Audit
Before publishing a build, DevExpress NuGet packages (along with test and demo apps) are tested against NuGet.org audit. NuGet.org obtains CVE/GHSA reports directly from the centralized GitHub Advisory Database. We use the .NET CLI commands such as dotnet list package --vulnerable --include-transitive to detect known vulnerabilities in third-party dependencies.
- NuGetAudit 2.0: Elevating Security and Trust in Package Management
- Central Package Management (CPM) & Overriding Package Versions
- Application Security — Project Dependency “Version Bumps” Demystified or Modern Security Realities in .NET / NuGet Ecosystem
Security Advisories and Product Update Process
We are not perfect and security-related issues may be introduced into an official DevExpress release. If we locate a potential security vulnerability in an official DevExpress release, we will publish a fix in the shortest possible time frame (usually our next minor product update). Once patched versions are ready for download/deployment, we update the DevExpress Security Advisory Bulletin and announce the security update via email and our website. Our security advisory describes the issue, lists affected products, and steps that must be taken to mediate future risk.
- DevExpress Security Advisory Bulletin
- Filter Security Advisories by Product/Build
- Supported DevExpress Product Versions
- Information Security | SDLC & Supply Chain-related Frequently Asked Questions
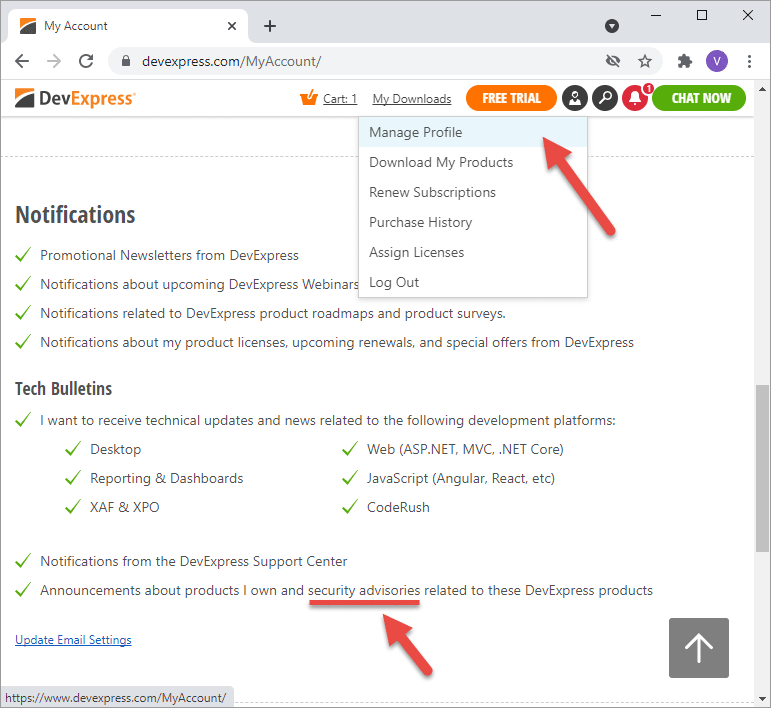
Note
We respect your privacy rights. To receive security-related advisories via email, you must update your DevExpress.com profile and authorize us to send you (or your authorized representative) security-related advisory email messages:
Best Practices
The DevExpress Security Guild - in collaboration with individual DevExpress development teams - has produced a series of security-related best practice help topics for your consideration. Whether you currently use DevExpress controls or are evaluating DevExpress products for a future project, the following resources should help you design and test your software application(s).
Multiple Platforms
- False Positive Vulnerabilities - Known alerts detected by various security scanners and services
- Suppress New Processes Initiated by .NET Controls
- Suppress Control Requests to Download Data from External URLs
- Safe Deserialization
- How to Use DevExpress Controls with Content Security Policy (CSP)
- Application Security — Project Dependency “Version Bumps” Demystified or Modern Security Realities in .NET / NuGet Ecosystem
- Application Security — Why One Does Not Simply Protect a Data Store Connection String and Other Login Credentials?
- Application Security — Stronger Hashes and Safer Passwords
- Modern Desktop Apps and Data Access Security
- Modern Desktop Apps and Their Complex Architectures
Web Controls
- Blazor Components – Security Considerations
- DevExtreme (Angular, React, Vue, and jQuery) Controls – Security Considerations
- ASP.NET Core Controls – Security Considerations
- ASP.NET Web Forms Controls – Security Considerations
- ASP.NET MVC Extensions – Security Considerations
- ASP.NET Bootstrap Controls – Security Considerations
WinForms and WPF Controls
Reporting
BI Dashboard
XAF - Cross-Platform .NET App UI & Web API Service
Full Source Code is Available
No matter what we do, how we do it, or how much time we invest, ultimate responsibility for quality and application-wide security lies with you and your organization. For this reason, we allow every organization to purchase full source code for all DevExpress components (full source code is available in the DevExpress Universal Subscription). Through source code review, you can fully evaluate/analyze our products and ensure that DevExpress components meet your organization’s security-related or quality-related requirements.
Should you have security-related questions or require additional guidance, please email management@devexpress.com. To explore our end-user license agreement and review the terms that govern use of all DevExpress products, please visit the following webpage: Licensing: EULAs and FAQ | DevExpress